The best VPN router needs to have great software with enough speed to keep up with modern connection speeds. Using one of the best virtual private networks (VPN) keeps you secure and helps you get around regional restrictions. You can set up a VPN on each device individually with support in Android and iOS and Mac, Windows, and Linux. The main problem is that it has to be set up on each device individually. The Asus RT-AX55 has the best balance of software customization with fast enough speeds for most people.
The Zyxel IPSec VPN Client is designed an easy 3-step configuration wizard to help remote employees to create VPN connections quicker than ever. The user-friendly interface makes it easy to install, configure and use. With Zyxel IPSec VPN Client, setting up a VPN connection is no longer a daunting task.
- Isgabrillo's hit the nail on the head for accessing the Cisco VPN Client. If you want an alternative, you can also look at the Shrew Soft VPN Client (free download) at shrew.net or The Greenbow at thegreenbow.com.
- The Cisco Easy VPN client feature eliminates much of the tedious configuration work by implementing the Cisco Unity Client protocol. This protocol allows most VPN parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, WINS server addresses, and split-tunneling flags, to be defined at a VPN server, such as a Cisco VPN 3000 series concentrator that is acting as an.
Best Overall: Asus RT-AX55
© Provided by Windows CentralIt can be a challenge to decide exactly how much speed you need for your home network, and there are a ton of routers that offer so much more than most of us will ever need. The Asus RT-AX55 has a great balance for people moving to Wi-Fi 6 for most of their important Wi-Fi devices. A phone or computer with Wi-Fi 6 will have no trouble achieving gigabit speeds thanks to an AX1800 connection.
Four antennas help this router provide enough coverage for large homes but can be expanded as a mesh thanks to AiMesh software included with most Asus routers. It's worth keeping in mind that for fast Wi-Fi 5 (802.11ac) devices with 3x3 MIMO, this router won't be able to deliver those max speeds due to only having a 2x2 setup. If you want to make the most of those devices with Wi-Fi 6 support, you'll need to consider an upgraded router that has very similar software.
Asus keeps its router software fairly standard across most of its range, and most Asus routers support VPN connections. This router will work with an OpenVPN client setup, which most VPN providers use and will allow for quick and easy setup. It also supports many other traffic management features you would expect in a modern router, such as MU-MIMO and adaptive QoS, to keep traffic moving well even with many connections.
Pros:
- Fast Wi-Fi 6 speeds
- AiProtection Classic includes free antivirus protection
- AiMesh allows for easy expansion
Cons:
- No 160MHz support
- Only dual-band
Best Overall
Asus RT-AX55
© Provided by Windows CentralA great intro to Wi-Fi 6
For Wi-Fi 6 devices, this router will offer great speeds, and consistency with the included Asus software making VPN setup a snap.
Best Value: Asus RT-AC66U B1
© Provided by Windows CentralThere are a ton of cheap routers available, but for most people, the sweet spot is right around AC1750. This allows for around 450Mbps at 2.4GHz and 1300Mbps at 5GHz on devices like a high-end notebook and desktop wireless hardware. The RT-AX66U from Asus offers this solid setup along with four Ethernet ports and dual USB ports. Three large antennas allow for solid coverage even in large homes.
AiProtection Pro is included with its advanced parental controls making this a powerful and flexible router for families. Asus has also included OpenVPN client support allowing for easy configuration with most VPN services. AiMesh allows for future coverage expansion with another Asus router if needed. This router isn't the fastest by a long stretch, but it should be a great upgrade over what's provided by their service provider for many people.
Pros:
- AC1750 speeds are enough for many
- 4 Ethernet ports
- Great software included
- 3x3 MIMO support
Cons:
- Aging design
- No Wi-Fi 6 support
Best Value
Asus RT-AC66U B1
© Provided by Windows CentralGreat software with enough speed and coverage
The RT-AC66U has plenty of speed for many people and a robust software range for security, privacy, and even mesh expansion.
Best Mesh System: Asus ZenWiFi AX XT8
© Provided by Windows CentralAll of the Asus Zen products have a nice design that manages to look very modern and clean without giving up on any functionality. The ZenWiFi AX XT8 comes with two mesh nodes connecting the Asus AiMesh software and easily covering substantial homes up to 5,500 square feet. If this isn't enough, any Asus router with AiMesh support can be used to expand coverage, though another tri-band ZenWiFi router is probably your best bet.
AX4200 speeds allow this system to easily keep up with gigabit connections with enough headroom for fast home networking. A 2.5G wan port adds support even for fast fiber internet connections or, more likely, compatibility with a fast wired network setup. There are three Ethernet ports on each unit as well to connect wired devices, and with its fast dedicated backhaul, it could replace the need for running Ethernet across your home.
Asus brings along its software with AiProtection Pro with advanced parental controls. Support for an OpenVPN client brings support for pretty much any VPN service with easy setup. With a VPN and AIProtection Pro, this can be a very secure and private mesh system.
Pros:
- AX4200 is fast enough for a gigabit connection
- 3 Ethernet per node with 2.5G WAN
- Works with AIMesh
- AiProtection Pro is included
Cons:
- Large nodes
Best Mesh System
Asus ZenWiFi AX XT8
 © Provided by Windows Central
© Provided by Windows CentralA fast Wi-Fi 6 mesh with AiMesh support
The Asus ZenWifi AX is a fast mesh system at AX4200 speeds with tri-band support, plenty of expansion options, and great software.
Best with custom software: Linksys WRT3200ACM
© Provided by Windows CentralFirst and foremost, this router will not work with your VPN service out of the box. If you like to have full control over your software and hardware over speed and value, the Linksys WRT3200ACM is a compelling product when installing something like DD-WRT. To be clear, it's possible to install this software on a lot of different routers, but this Linksys router is open-source ready and has a processor powerful enough to not get bogged down.
Once the software is taken care of, the WRT3200ACM's 1.8Ghz dual-core CPU pushes high Wi-Fi 5 speeds at AC3200 and four gigabit Ethernet connections. With four antennas and MU-MIMO management, consistency is kept high, and buffering is minimized. The classic blue and black design brings back memories of the popular WRT54G and feels at home in any computer room. This isn't a slow router, but with its aging dual-band connection, it's not as fast as most newer routers at this price.
It has to be stressed that custom software on the router will not be supported by Linksys' customer support, and the user will be responsible for troubleshooting problems. Please be sure you are comfortable with this before choosing this as your VPN router.
Pros:
- AC3200 speeds are fast enough for most
- USB 3.0 and ESATA for storage
- MU-MIMO
- Classic design
Cons:
- Custom software required
- No customer support for software
- Expensive for the speed
Best with custom software
Linksys WRT3200ACM
© Provided by Windows CentralCustom software puts you in control
While the WRT-3200 isn't as fast as newer routers, its custom software allows for complete control if you're willing to tinker.
Best Software: Synology RT2600ac
© Provided by Windows CentralThe Synology RT2600ac doesn't look too impressive right at first, but thanks to its amazing software features and great support, it stands out as one of the best choices for those that want to be in full control of their network. No doubt, it's a couple of years old now and doesn't support Wi-Fi 6, but it has a powerful 802.11ac Wave 2 setup allowing for a 160MHz channel and delivers speeds up to AC2600 with 1.73Gbps at 5GHz and an impressive 800Mbps at 2.4GHz. Despite the lack of tri-band, this is one the best Wi-Fi 5 routers around.
Synology's software includes OpenVPN support and can be configured as a VPN client that will work with most VPN providers. It also comes with other great software features like robust parental controls, making this a great choice for families. It has one dedicated WAN port and four LAN Ethernet ports though one can be used for dual WAN. This router even has a mesh option with the MR2200ac router.
Pros:
- Fast Wi-Fi 5 speeds
- Great software from Synology
- Parental controls
- Mesh expansion available
Cons:
- Expensive for the speed
- No Wi-Fi 6 support
Best Software
Synology RT2600ac
© Provided by Windows CentralGreat software for those that want full control
The Synology RT2600ac is great for those that want great software over everything else with solid WI-Fi 5 speeds to back it up.
Best for Gaming: Asus RT-AX82U
© Provided by Windows CentralThe Asus RT-AX82U has a unique design with full RGB control that's a compliment to any gaming setup. Rest assured that the RGB lighting can be completely disabled if you prefer. This router comes with a dual-band AX5400 wireless setup with these high speeds thanks to a 160MHz 5GHz channel. For devices that support Wi-Fi 6, this should have no trouble keeping up with a gigabit connection.
This router also has four Ethernet ports, with one specifically allocated for gaming. If you have a gaming PC or play competitively on your Xbox, this is the preferred port to use. Gaming software is also included and can be controlled with the Asus router app to ensure the right devices and applications have a priority connection. Don't forget that gaming over a VPN can introduce extra lag, so it's probably a good idea to create an exception for gaming machines.
Once again, Asus has a robust set of software included with this router, including its AiProtection Pro software for enhanced security and parental controls. This software also supports creating a mesh network with other Asus routers thanks to AiMesh. Naturally, Asus also has VPN client support with OpenVPN, which should be quick and easy to set up with most VPN providers.
Pros:
- Very fast AX5400 speeds
- AiMesh compatible
- Optimized gaming software
- AiProtection Pro included
Cons:
- No 2.5G WAN
Best for Gaming

Asus RT-AX82U
© Provided by Windows CentralFast hardware with gaming software
The Asus RT-AX82U is a fast Wi-Fi 6 router with AX5400 speeds, free security software, gaming optimizations, and AiMesh support.
Bottom line
Keep in mind that you don't necessarily need a router with VPN support to use a VPN. You can install a VPN on any modern operating system, and setting up a VPN on Windows 10 is reasonably easy to accomplish. Most VPN services also have downloadable software that makes it extremely easy. Overall, the Asus RT-AX55 is one of the best routers to use with a VPN thanks to its accessible software and fast hardware with plenty of modern features.
Credits — The team that worked on this guide
Samuel Contreras When Samuel is not writing about networking at Windows Central, he spends most of his time researching computer components and obsessing over what CPU goes into the ultimate Windows 98 computer. It's the Pentium 3.
Table Of Contents
Configuring a VPN Using Easy VPN and an IPSec Tunnel
The Cisco 870 series routers support the creation of Virtual Private Networks (VPNs).
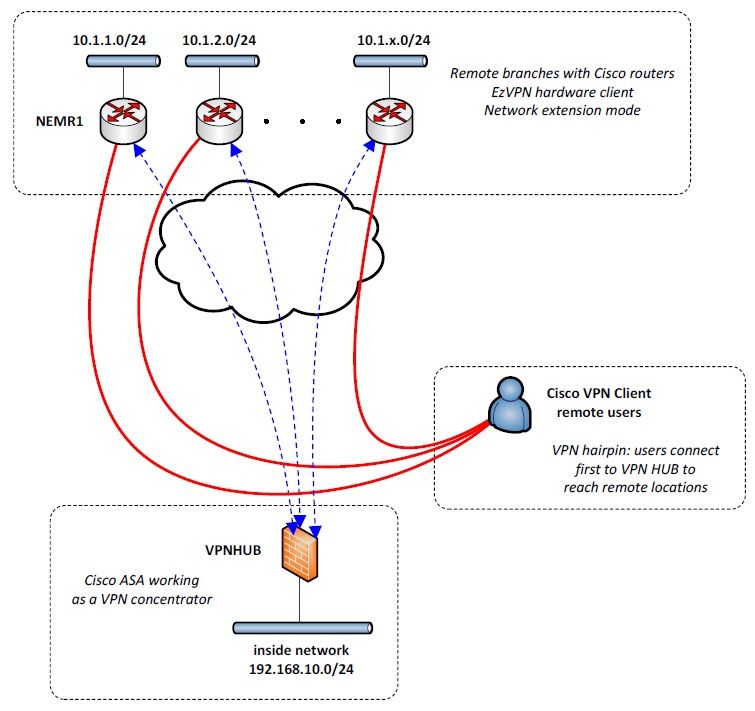
Cisco routers and other broadband devices provide high-performance connections to the Internet, but many applications also require the security of VPN connections which perform a high level of authentication and which encrypt the data between two particular endpoints.
Two types of VPNs are supported—site-to-site and remote access. Site-to-site VPNs are used to connect branch offices to corporate offices, for example. Remote access VPNs are used by remote clients to log in to a corporate network.
The example in this chapter illustrates the configuration of a remote access VPN that uses the Cisco Easy VPN and an IPSec tunnel to configure and secure the connection between the remote client and the corporate network. Figure 6-1 shows a typical deployment scenario.
Note The material in this chapter does not apply to Cisco 850 series routers. Cisco 850 series routers do not support Cisco Easy VPN.
Figure 6-1 Remote Access VPN Using IPSec Tunnel
Hewland gearbox. Remote, networked users | |
2 | VPN client—Cisco 870 series access router |
Router—Providing the corporate office network access | |
4 | VPN server—Easy VPN server; for example, a Cisco VPN 3000 concentrator with outside interface address 210.110.101.1 |
Corporate office with a network address of 10.1.1.1 | |
6 | IPSec tunnel |
Cisco Easy VPN
The Cisco Easy VPN client feature eliminates much of the tedious configuration work by implementing the Cisco Unity Client protocol. This protocol allows most VPN parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, WINS server addresses, and split-tunneling flags, to be defined at a VPN server, such as a Cisco VPN 3000 series concentrator that is acting as an IPSec server.
An Easy VPN server-enabled device can terminate VPN tunnels initiated by mobile and remote workers who are running Cisco Easy VPN Remote software on PCs. Easy VPN server-enabled devices allow remote routers to act as Easy VPN Remote nodes.
The Cisco Easy VPN client feature can be configured in one of two modes—client mode or network extension mode. Client mode is the default configuration and allows only devices at the client site to access resources at the central site. Resources at the client site are unavailable to the central site. Network extension mode allows users at the central site (where the VPN 3000 series concentrator is located) to access network resources on the client site.
After the IPSec server has been configured, a VPN connection can be created with minimal configuration on an IPSec client, such as a supported Cisco 870 series access router. When the IPSec client initiates the VPN tunnel connection, the IPSec server pushes the IPSec policies to the IPSec client and creates the corresponding VPN tunnel connection.
Note The Cisco Easy VPN client feature supports configuration of only one destination peer. If your application requires creation of multiple VPN tunnels, you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on both the client and the server.
Configuration Tasks
Perform the following tasks to configure your router for this network scenario:
•Configure the IKE Policy
•Configure Group Policy Information
•Apply Mode Configuration to the Crypto Map
•Enable Policy Lookup
•Configure IPSec Transforms and Protocols
Rv320 Easy Vpn Client
•Configure the IPSec Crypto Method and Parameters
•Apply the Crypto Map to the Physical Interface
•Create an Easy VPN Remote Configuration
An example showing the results of these configuration tasks is provided in the 'Configuration Example' section.
Note The procedures in this chapter assume that you have already configured basic router features as well as PPPoE or PPPoA with NAT, DCHP and VLANs. If you have not performed these configurations tasks, see Chapter 1 'Basic Router Configuration,'Chapter 3 'Configuring PPP over Ethernet with NAT,'Chapter 4 'Configuring PPP over ATM with NAT,' and Chapter 5 'Configuring a LAN with DHCP and VLANs' as appropriate for your router.
Note The examples shown in this chapter refer only to the endpoint configuration on the Cisco 870 series router. Any VPN connection requires both endpoints be configured properly to function. See the software configuration documentation as needed to configure VPN for other router models.
Configure the IKE Policy
Perform these steps to configure the Internet Key Exchange (IKE) policy, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto isakmp policypriority Example: | Creates an IKE policy that is used during IKE negotiation. The priority is a number from 1 to 10000, with 1 being the highest. Also enters the Internet Security Association Key and Management Protocol (ISAKMP) policy configuration mode. |
Step 2 | encryption {des | 3des | aes | aes 192 | aes 256} Example: | Specifies the encryption algorithm used in the IKE policy. The example specifies 168-bit data encryption standard (DES). |
Step 3 | hash {md5 | sha} Example: | Specifies the hash algorithm used in the IKE policy. The example specifies the Message Digest 5 (MD5) algorithm. The default is Secure Hash standard (SHA-1). |
Step 4 | authentication {rsa-sig | rsa-encr | pre-share} Automatically post RSS feeds to Twitter, Facebook, and LinkedIn. Effortlessly feed news, blog posts and photos to social media. You can let your readers know what you are up to by tweeting about it. Twitter feedee. The latest tweets from @Twitter. Example: | Specifies the authentication method used in the IKE policy. The example specifies a pre-shared key. |
Step 5 | group {1 | 2 | 5} Example: | Specifies the Diffie-Hellman group to be used in an IKE policy. |
Step 6 | lifetime seconds Example: | Specifies the lifetime, 60-86400 seconds, for an IKE security association (SA). |
Step 7 | exit Example: | Exits IKE policy configuration mode, and enters global configuration mode. |
Configure Group Policy Information
Perform these steps to configure the group policy, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto isakmp client configuration group {group-name | default} Example: | Creates an IKE policy group containing attributes to be downloaded to the remote client. Also enters the Internet Security Association Key and Management Protocol (ISAKMP) group policy configuration mode. |
Step 2 | key name Example: | Specifies the IKE pre-shared key for the group policy. |
Step 3 | dns primary-server Example: | Specifies the primary Domain Name System (DNS) server for the group. Note You may also want to specify Windows Internet Naming Service (WINS) servers for the group by using the wins command. |
Step 4 | domain name Example: | Specifies group domain membership. |
Step 5 | exit Example: | Exits IKE group policy configuration mode, and enters global configuration mode. |
Step 6 | ip local pool {default | poolname} [low-ip-address [high-ip-address]] Example: | Specifies a local address pool for the group. For details about this command and additional parameters that can be set, see the . |
Apply Mode Configuration to the Crypto Map
Perform these steps to apply mode configuration to the crypto map, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto map map-name isakmp authorization list list-name Example: | Applies mode configuration to the crypto map and enables key lookup (IKE queries) for the group policy from an authentication, authorization, and accounting (AAA) server. |
Step 2 | crypto map tag client configuration address [initiate | respond] Example: | Configures the router to reply to mode configuration requests from remote clients. |
Enable Policy Lookup
Perform these steps to enable policy lookup through AAA, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | aaa new-model Example: | Enables the AAA access control model. |
Step 2 | aaa authentication login {default |list-name}method1[method2..] Example: | Specifies AAA authentication of selected users at login, and specifies the method used. This example uses a local authentication database. You could also use a RADIUS server for this. For details, see the and . |
Step 3 | aaa authorization {network | exec | commands level| reverse-access | configuration} {default |list-name} [method1[method2..]] Example: | Specifies AAA authorization of all network-related service requests, including PPP, and specifies the method of authorization. This example uses a local authorization database. You could also use a RADIUS server for this. For details, see the and . |
Step 4 | usernamename {nopassword | passwordpassword | password encryption-typeencrypted-password} Example: | Establishes a username-based authentication system. This example implements a username of Cisco with an encrypted password of Cisco. |
Configure IPSec Transforms and Protocols
A transform set represents a certain combination of security protocols and algorithms. During IKE negotiation, the peers agree to use a particular transform set for protecting data flow.
During IKE negotiations, the peers search in multiple transform sets for a transform that is the same at both peers. When such a transform set is found, it is selected and applied to the protected traffic as a part of both peers' configurations.
Perform these steps to specify the IPSec transform set and protocols, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto ipsec transform-set transform-set-name transform1 [transform2] [transform3] [transform4] Example: | Defines a transform set—an acceptable combination of IPSec security protocols and algorithms. See the Cisco IOS Security Command Reference for detail about the valid transforms and combinations. |
Step 2 | crypto ipsec security-association lifetime {secondsseconds | kilobyteskilobytes} Example: | Specifies global lifetime values used when IPSec security associations are negotiated. See the Cisco IOS Security Command Reference for details. |
Note With manually established security associations, there is no negotiation with the peer, and both sides must specify the same transform set.
Configure the IPSec Crypto Method and Parameters
A dynamic crypto map policy processes negotiation requests for new security associations from remote IPSec peers, even if the router does not know all the crypto map parameters (for example, IP address).
Perform these steps to configure the IPSec crypto method, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto dynamic-mapdynamic-map-name dynamic-seq-num Example: | Creates a dynamic crypto map entry and enters crypto map configuration mode. See the Cisco IOS Security Command Reference for more detail about this command. |
Step 2 | set transform-set transform-set-name [transform-set-name2..transform-set-name6] Example: | Specifies which transform sets can be used with the crypto map entry. |
Step 3 | reverse-route Example: | Creates source proxy information for the crypto map entry. See the Cisco IOS Security Command Reference for details. |
Step 4 | exit Example: | Returns to global configuration mode. |
Step 5 | crypto map map-name seq-num [ipsec-isakmp] [dynamicdynamic-map-name] [discover] [profileprofile-name] Example: | Creates a crypto map profile. |
Apply the Crypto Map to the Physical Interface
Cisco Easy Vpn Client Download
The crypto maps must be applied to each interface through which IP Security (IPSec) traffic flows. Applying the crypto map to the physical interface instructs the router to evaluate all the traffic against the security associations database. With the default configurations, the router provides secure connectivity by encrypting the traffic sent between remote sites. However, the public interface still allows the rest of the traffic to pass and provides connectivity to the Internet.
Free Vpn Client Software
Perform these steps to apply a crypto map to an interface, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | interface type number Example: | Enters the interface configuration mode for the interface to which you want the crypto map applied. |
Step 2 | crypto map map-name Example: | Applies the crypto map to the interface. See the Cisco IOS Security Command Reference for more detail about this command. |
Step 3 | exit Example: | Returns to global configuration mode. |
Create an Easy VPN Remote Configuration
The router acting as the IPSec remote router must create an Easy VPN remote configuration and assign it to the outgoing interface.
Perform these steps to create the remote configuration, beginning in global configuration mode:
Easy Vpn Client Configuration
Purpose | ||
|---|---|---|
Step 1 | crypto ipsec client ezvpnname Example: | Creates a Cisco Easy VPN remote configuration, and enters Cisco Easy VPN remote configuration mode. |
Step 2 | group group-name key group-key Example: | Specifies the IPSec group and IPSec key value for the VPN connection. |
Step 3 | peer {ipaddress | hostname} Example: | Specifies the peer IP address or hostname for the VPN connection. Note A hostname can be specified only when the router has a DNS server available for hostname resolution. |
Step 4 | mode {client | network-extension | network extension plus} Example: | Specifies the VPN mode of operation. |
Step 5 | exit Example: | Returns to global configuration mode. |
Step 6 | interfacetype number Example: | Enters the interface configuration mode for the interface to which you want the Cisco Easy VPN remote configuration applied. Note For routers with an ATM WAN interface, this command would be interface atm 0. |
Step 7 | crypto ipsec client ezvpn name [outside | inside] Example: | Assigns the Cisco Easy VPN remote configuration to the WAN interface, causing the router to automatically create the NAT or port address translation (PAT) and access list configuration needed for the VPN connection. |
Step 8 | exit Example: | Returns to global configuration mode. |
Verifying Your Easy VPN Configuration
Configuration Example
Cisco Easy Vpn Client Download Windows 10
The following configuration example shows a portion of the configuration file for the VPN and IPSec tunnel described in this chapter.
